IT infrastructure optimization is an essential strategy for businesses of all sizes. It involves analyzing, evaluating, and improving your existing IT infrastructure to enhance performance, reduce costs, and increase efficiency. This can include a range of tasks such as virtualization, cloud computing, network security enhancements, and data center consolidation. By adopting best practices in IT infrastructure optimization, organizations can streamline operations, improve agility, and gain a competitive edge. A well-optimized infrastructure ensures reliable access to applications and data, supports business growth, and minimizes the risk of downtime.
Securing Your Systems Against Attacks
In today's digital landscape/connected world/ever-evolving technological environment, businesses of all sizes/shapes/scales face increasingly sophisticated/growing/mounting cybersecurity threats. To effectively combat these risks, organizations must implement robust cybersecurity solutions/threat mitigation strategies/defense mechanisms. These solutions encompass a wide range/spectrum/variety of tools and technologies designed to protect against data breaches/malware attacks/ransomware infections.
Effective threat detection is crucial/essential/fundamental to any comprehensive cybersecurity strategy. Advanced security software/Threat intelligence platforms/Security Information and Event Management (SIEM) systems can help organizations identify/detect/recognize potential threats in real time, allowing for proactive response/swift mitigation/immediate action. By leveraging these solutions, businesses can strengthen their defenses/reduce their vulnerability/minimize the impact of cyberattacks.
- Implementing multi-factor authentication/Enforcing strong password policies/Utilizing secure network protocols
- Conducting regular security assessments/Staying informed about emerging threats/Training employees on cybersecurity best practices
- Developing a comprehensive incident response plan/Having a clear data backup and recovery strategy/Partnering with reputable cybersecurity vendors
Transitioning to Cloud Computing and Management
Cloud computing migration and management is a dynamic process that requires careful planning and execution. Organizations seeking to leverage the benefits of cloud computing must carefully assess their current infrastructure, applications, and business requirements. A detailed migration strategy should specify the scope of the migration, the selected cloud platform, and the deployment timeline.
- Robust infrastructure management is essential for ensuring the availability of cloud-based applications.
- Monitoring cloud resources and pinpointing potential issues in a timely manner is paramount.
Successful cloud computing migration and management require here a skilled team with expertise in cloud technologies, security best practices, and platform administration.
Business Intelligence and Data Analytics
In today's data-driven realm, companies of all sizes are harnessing the power of data analytics to make informed decisions. Data analytics involves the technique of extracting, structuring, and visualizing data to uncover hidden insights. Business intelligence, on the other hand, focuses on utilizing these data insights into {actionableplans that drive success. By merging data analytics and business intelligence, organizations can gain a comprehensive understanding of their operations, enhance efficiency, and make informed decisions to achieve their objectives.
Network Architecture and Deployment
Network design and implementation is a multifaceted process that involves architecting robust and scalable networks to meet specific organizational needs. It encompasses evaluating current infrastructure, identifying objectives, selecting appropriate hardware and software components, and creating detailed documentation. A well-designed network should be reliable, capable of handling communication effectively, and scalable to accommodate future growth. The implementation phase involves configuring network devices, testing connectivity, and assigning user accounts and permissions.
- Essential factors in network design include security, performance, scalability, and cost-effectiveness.
- Recommended guidelines should be followed throughout the design and implementation process to ensure a robust network infrastructure.
- Network monitoring and management are vital for maintaining optimal network performance and identifying potential issues proactively.
Customer Support and Technology Service Delivery
Effective IT Service Desk is a fundamental pillar of successful IT Service Management . A well-structured Support Team not only resolves routine user problems but also reactively identifies and addresses potential challenges in the technology environment. By streamlining the workflow for request management, organizations can enhance user satisfaction, minimize downtime, and ultimately foster a more seamless work environment.
- Fundamental components of effective IT Service Desk include: communication, collaboration, knowledge management, and a customer-centric approach.
- Automation plays a vital role in enhancing the Service Desk 's operations, allowing them to handle requests more efficiently.
- Ongoing optimization is essential for IT Service Desk to evolve with the changing requirements of the organization and its users.
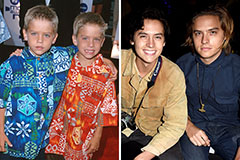 Dylan and Cole Sprouse Then & Now!
Dylan and Cole Sprouse Then & Now! Alexa Vega Then & Now!
Alexa Vega Then & Now! James Van Der Beek Then & Now!
James Van Der Beek Then & Now! Mason Reese Then & Now!
Mason Reese Then & Now!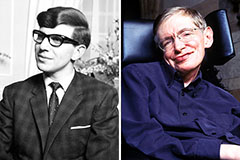 Stephen Hawking Then & Now!
Stephen Hawking Then & Now!